Table of Contents
Master Data Privacy Compliance and Reduce Risk Today
Data privacy compliance requires organizations to protect personal data while meeting evolving global regulations. A structured approach covering discovery, classification, governance, controls, and continuous monitoring helps reduce risk. By adopting best practices and leveraging governance platforms, businesses can streamline compliance efforts, strengthen customer trust, and remain prepared for audits and regulatory changes.
What is Data Privacy Compliance?
Every organization that deals with user or customer information must ensure it has adequate measures in place to guarantee this sensitive data is protected. It sounds simple enough. Many might presume that all you need to do to be compliant is store the data in your care in a secure location, well out of reach of cyber crooks.
Unfortunately, data privacy compliance is far from straightforward.
As well as protecting data from third-party threats, organizations must ensure that only people with adequate permissions have access to it.
For example, a single complaints handling team might include seven staff members. For the purposes of this scenario, let’s imagine only two of them have permission to access customer addresses and telephone numbers. However, every member of the team will require access to customer names and call records. In many ways, data privacy compliance is as much about permission as it is about protection.
Furthermore, data governance teams aren’t required to follow just one law, there are many. Of course, the most famous is the EU’s General Data Protection Regulation (GDPR), but new regulations are being developed all the time.
Each law is different, so it’s down to the data governance team to determine what they should be doing based on the data they handle—and that’s just external compliance. Internally, there are countless specific regulations concerning the use, storage, and management of customer data.
Learn more about our easy-to-use discovery platform and data governance tool kit. Get in touch today and find out how OvalEdge can streamline your data governance strategy.
Understanding Privacy Compliance 2026
Privacy compliance now spans global regulations such as GDPR, CCPA, and India’s new Digital Personal Data Protection (DPDP) Rules 2025, all of which require clear notices, explicit consent, and robust security safeguards. Modern data privacy and compliance programs must also address AI use, cross‑border data transfers, and third‑party vendor risks to avoid fines, reputational damage, and data breaches. **
Organizations often ask, “is data compliance straightforward?” In practice, it is not: regulations change frequently, data is scattered across systems, and legacy manual controls rarely scale effectively. This is why platforms such as OvalEdge data governance and its integrated data catalog help centralize policies, lineage, and access controls, making privacy compliance more manageable and auditable.
Common Challenges: Is Data Compliance Straightforward
Despite increasing automation, many organizations still discover that data compliance is far from straightforward due to several recurring challenges:
- Data sprawl and unstructured repositories make it difficult to locate all personal data, leaving blind spots that can undermine regulatory responses to data‑subject requests. A governed data catalog helps surface these hidden datasets and connect them with appropriate policies.
- Siloed tools and manual spreadsheets create fragmented views of consent, retention, and access logs, which are hard to reconcile during audits. By consolidating metadata, business glossaries, and lineage in a centralized platform like OvalEdge privacy teams can generate consistent, traceable evidence for regulators and internal stakeholders.
- Third‑party vendors and cloud providers introduce additional risk, which is why 2025 privacy guidance stresses continuous vendor assessment and contract‑level security requirements. Integrating vendor data flows into your data governance framework ensures that external processing is visible and controlled.
Addressing these issues systematically helps transform privacy compliance into a repeatable process instead of a one‑off project.
How Can Compliance Issues Impact Your Business?
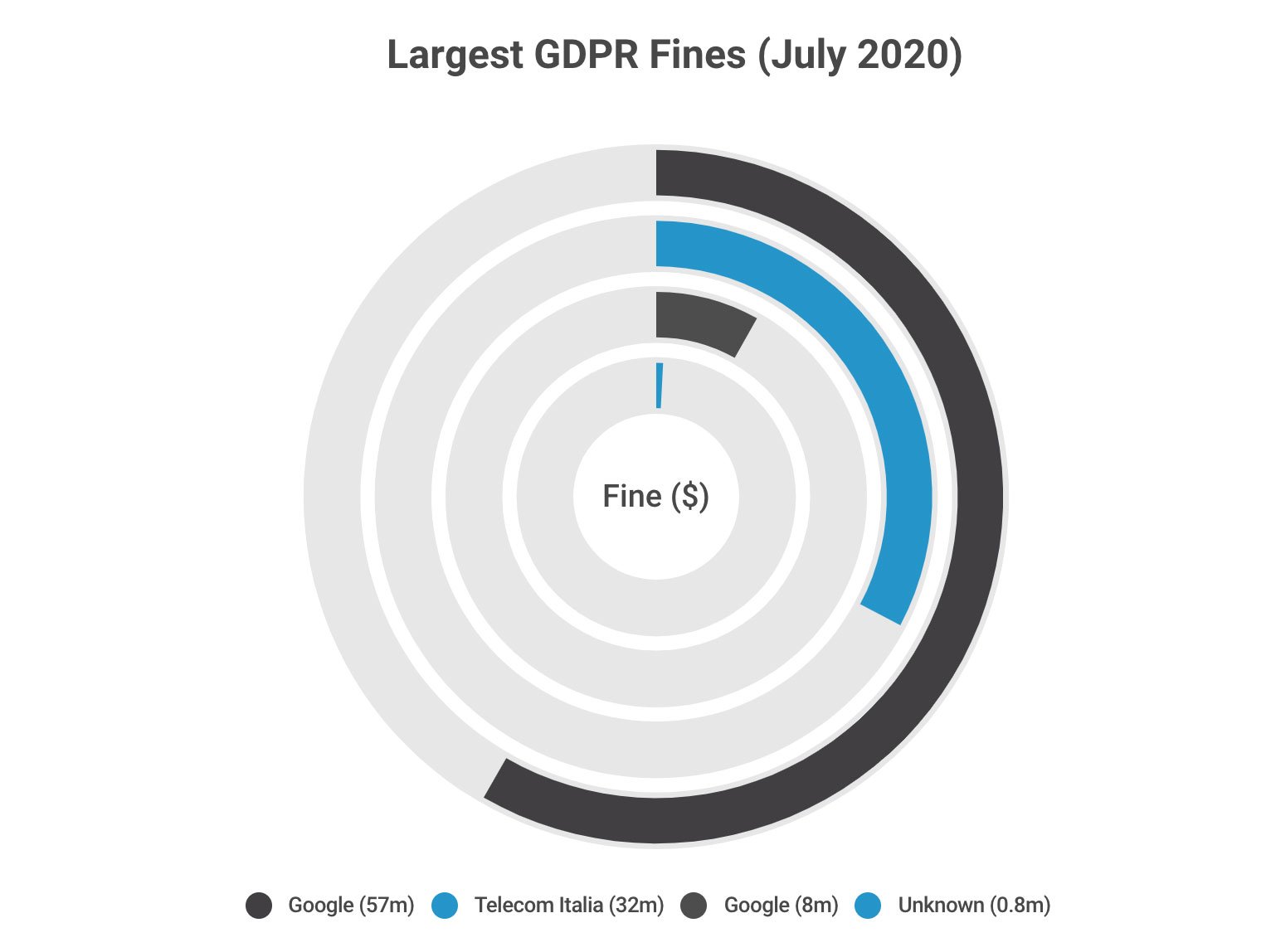
First and foremost, failing to enforce compliance can cost you a lot of money. The penalties for ignoring the world’s most stringent data privacy regulations are extreme.
Failure to follow GDPR rules can result in a maximum fine of €20 million ($24 million) or 4% of annual global turnover, while intentionally violating the California Consumer Privacy Act can incur penalties of $7,500 for per violation.
Data privacy compliance is as much about permission as it is about protection.
In the middle east, Dubai’s DIFC Data Protection Law’s administrative fines range from $20,000 to $100,000. However, this is just the tip of the iceberg. There are numerous other regulations concerning data use across the globe that could require compliance measures whether or not you operate in the jurisdiction.
You can be fined just for mishandling data from users based in the countries where a certain law is active, and these fines are not just threats. Take GDPR for example:
Building Trust
The other area that compliance can impact greatly is consumer trust. If your organization develops a reputation as a company that flouts data privacy regulations this will have a very negative impact on your standing within your industry.
Data privacy is becoming more and more important to consumers and with this heightened awareness comes a greater need for data owners to honor the wishes of their customers. Beyond regulatory requirements, data privacy compliance is an ethical issue that builds trust in an organization.
Related: 3 Data Privacy Compliance Challenges that can be solved with OvalEdge
Data Privacy Compliance: Who is it for?
Although compliance issues can have company-wide implications, data privacy compliance is the responsibility of an organization’s data governance team—primarily data protection officers.
It is the obligation of the data governance team to check that all personally identifiable information (PII), especially metadata, is managed, categorized, and secured correctly.
Common data privacy compliance regulations and requirements
As organizations increasingly rely on data to drive business decisions, complying with global privacy regulations has become a strategic necessity rather than just a legal obligation. Data privacy compliance ensures that companies collect, process, store, and share personal information in ways that respect individual rights and meet regulatory expectations. Modern frameworks emphasize transparency, accountability, and strong security controls to reduce risk and build customer trust. Below are the most important regulations and the core requirements organizations should understand when building a robust privacy program.
1. General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR) is widely considered the gold standard for data privacy laws. Introduced by the European Union, it applies not only to organizations located in the EU but also to any business worldwide that processes the personal data of EU residents. GDPR focuses heavily on user rights, lawful processing, and organizational accountability. Because of its strict enforcement and high penalties, many companies use GDPR as the baseline for their global privacy strategy.
Key requirements:
- Obtain clear and explicit user consent
- Ensure personal data accuracy and integrity
- Implement strong technical and organizational security controls
- Enable data subject rights such as access, correction, and deletion
- Maintain detailed records of processing activities
Penalties: Non-compliance can result in fines of up to 4% of global annual turnover or €20 million, whichever is higher.
2. California Consumer Privacy Act (CCPA)
The California Consumer Privacy Act (CCPA) is a landmark U.S. privacy law that gives California residents greater visibility and control over how their personal data is collected and used. It primarily targets for-profit organizations that meet certain revenue or data-volume thresholds. CCPA emphasizes consumer transparency and opt-out rights, making it particularly important for companies operating in or serving customers in the United States.
Key requirements:
- Provide clear notice about data collection and usage practices
- Allow consumers to request access to their personal data
- Enable deletion requests where applicable
- Offer a clear opt-out mechanism for the sale of personal information
- Maintain reasonable security procedures to protect data
3. Health Insurance Portability and Accountability Act (HIPAA)
HIPAA is a sector-specific regulation that governs how protected health information (PHI) is handled in the United States healthcare ecosystem. It applies to healthcare providers, insurers, clearinghouses, and their business associates. Because medical data is highly sensitive, HIPAA places strong emphasis on administrative, physical, and technical safeguards to prevent unauthorized access or disclosure.
Key requirements:
- Safeguard medical records and PHI
- Implement administrative, physical, and technical controls
- Restrict and monitor access to sensitive health data
- Maintain audit logs and activity monitoring
- Establish formal breach notification procedures
4. India Digital Personal Data Protection (DPDP) Act
India’s Digital Personal Data Protection (DPDP) Act represents a major step forward in the country’s privacy landscape. The law applies to organizations processing digital personal data of individuals in India and focuses on consent-driven data processing and accountability. As India’s digital economy expands, DPDP compliance is becoming increasingly important for both domestic and global companies operating in the region.
Key requirements:
- Obtain clear, affirmative user consent
- Collect data only for specified and lawful purposes
- Provide individuals with rights to access, correct, and erase data
- Implement reasonable security safeguards
- Report certain categories of data breaches
Steps for Master Data Privacy Compliance
Building a strong data privacy compliance program requires a structured, step-by-step approach. Organizations must move beyond ad hoc efforts and implement a repeatable process that ensures personal data is discovered, protected, governed, and continuously monitored. Follow the steps below to master data privacy compliance and reduce regulatory risk.
Step 1: Discover and Inventory Personal Data
The foundation of any privacy program is visibility. Organizations must first understand what personal data they collect, where it resides, and how it flows across systems. Without a comprehensive data inventory, applying controls or responding to regulatory requests becomes extremely difficult.
Key actions:
- Scan structured and unstructured data sources
- Identify personal and sensitive data elements
- Map data flows across systems and regions
- Maintain a centralized data inventory
- Continuously update the data catalog
Step 2: Classify Data and Assess Risk
After discovery, data should be classified based on sensitivity and regulatory scope. Classification helps prioritize protection efforts and enables risk-based decision-making. A formal risk assessment highlights high-exposure areas that require immediate attention.
Key actions:
- Apply sensitivity labels (PII, PHI, financial data)
- Map data to applicable regulations
- Conduct privacy impact assessments (PIA/DPIA)
- Identify high-risk processing activities
- Document risks and mitigation plans
Step 3: Define Privacy Policies and Governance
Clear policies and governance structures ensure consistent handling of personal data across the organization. This step establishes accountability and aligns legal, security, and data teams around common standards.
Key actions:
- Establish enterprise privacy policies
- Define data handling standards
- Assign ownership (DPO, privacy team, data stewards)
- Create retention and deletion policies
- Align governance with regulatory requirements
Step 4: Implement Technical and Organizational Controls
With policies in place, organizations must enforce them through strong controls. A combination of preventive, detective, and corrective safeguards helps protect data throughout its lifecycle.
Key actions:
- Encrypt sensitive data at rest and in transit
- Implement role-based access controls (RBAC)
- Enable multi-factor authentication
- Monitor data access and usage
- Apply masking or tokenization where needed
Step 5: Operationalize Data Subject Rights (DSAR)
Modern privacy laws require organizations to respond quickly to individual rights requests. Building automated, scalable workflows for DSAR fulfillment is critical to maintaining compliance and avoiding penalties.
Key actions:
- Establish DSAR intake channels
- Verify requester identity
- Locate user data across systems
- Fulfill access, deletion, and correction requests
- Track and report request SLAs
Step 6: Prepare a Data Breach Response Plan
Even mature organizations face security incidents. Regulators expect companies to have a documented and tested breach response process that enables rapid containment and notification.
Key actions:
- Define incident response procedures
- Classify breach severity
- Enable rapid detection and containment
- Prepare regulatory notification workflows
- Conduct periodic breach simulations
Step 7: Train Employees and Build Privacy Culture
Technology alone cannot ensure compliance. Employees must understand their responsibilities when handling personal data. Continuous training helps reduce human error and embeds privacy into everyday operations.
Key actions:
- Conduct mandatory privacy training
- Provide role-based guidance
- Promote privacy-by-design practices
- Run awareness and phishing exercises
- Track training completion
Step 8: Monitor, Audit, and Continuously Improve
Data privacy compliance is an ongoing journey. Organizations should continuously monitor controls, audit processes, and adapt to evolving regulations and business changes to remain audit-ready.
Key actions:
- Monitor compliance KPIs
- Perform regular privacy audits
- Review data access patterns
- Update controls as regulations evolve
- Maintain audit-ready documentation
Best Practices to Strengthen Privacy Compliance
To build resilient privacy compliance in 2026 and beyond, organizations are increasingly focusing on the following best practices:
- Adopt a structured data privacy framework that aligns legal, security, and data governance teams around shared policies, roles, and escalation paths. Mapping these policies to data assets within the OvalEdge data governance platform ensures they are implemented consistently.
- Implement data minimization and purpose limitation so that only the data truly needed for business processes is collected and retained, reducing risk and storage costs. Coupling these rules with catalog‑driven retention policies helps automate deletion and archival actions when legal retention periods expire.
- Educate employees continuously on privacy risks, phishing, and safe data handling, as human error remains a leading cause of breaches and compliance failures. Data stewards and owners defined in a governance model can act as local champions who embed data privacy and compliance into everyday workflows.
By following these practices and leveraging governance‑ready platforms, organizations make data privacy and compliance an everyday discipline rather than an annual scramble before audits
Implementing Data Privacy Compliance Protocols—Call in the Experts
The problem many organizations face is ensuring all the data they have in their care is managed correctly. Compliance in many ways is a data management issue, it’s about ensuring only correct metadata is collected and that this data is only made visible to the right users.
However, encrypting and managing data from thousands, hundreds of thousands or even millions of people is no small feat. On top of this, there needs to be a facility in place that enables user requests to delete information to be carried out quickly and efficiently.
Encrypting data is the easy part. The difficult bit is finding specific data from countless databases and archives.
The OvalEdge Solution
We give our clients access to a single dashboard that enables them to comply with regulations like GDPR and locate data from hundreds of databases, or even a data lake. This enables data governance teams to monitor PII across an organization.
Here’s how it works:
- We create a centralized repository of all your metadata
- Using AI, we identify all the PII
- You can then query hundreds of databases or a data lake on demand using HPII proprietary technology
- You reporting mechanism is centralized
- Now, you can automate workflow and processes for collection or deletion of data based on regulatory requirements
Learn more about our easy-to-use discovery platform and data governance tool kit. Get in touch today and find out how OvalEdge can streamline your data governance strategy.
FAQs
1. What is privacy compliance?
Privacy compliance is the process of ensuring that an organization collects, uses, stores, and shares personal data in accordance with applicable laws and standards such as GDPR, CCPA, and DPDP Rules 2025. It typically combines legal requirements with technical controls, policies, and documentation.
2. Is data compliance straightforward for most companies?
No, data compliance is rarely straightforward because data is distributed across multiple systems, regulations change frequently, and manual controls do not scale. Many organizations therefore, rely on governance platforms and automation to centralize evidence, monitoring, and reporting.
3. How are data privacy and compliance connected?
Data privacy and compliance are closely linked: privacy defines how personal data should be protected and used ethically, while compliance ensures adherence to the specific rules set by regulators. A strong program integrates both, using governance tools to align data policies, security controls, and business processes.
4. Which regulations are most important for privacy compliance in 2026?
Key regulations in 2025 include the EU’s GDPR, California’s CCPA, and India’s DPDP Act and Rules 2025, alongside sector‑specific requirements like HIPAA and financial‑services standards. Organizations operating globally often need a harmonized framework that can satisfy multiple regimes simultaneously.
5. How can OvalEdge help improve data privacy and compliance?
OvalEdge supports privacy compliance by providing an integrated data catalog and governance solution that maps data assets, lineage, and business rules in one place. This visibility enables organizations to implement retention policies, support subject‑rights requests, and demonstrate control effectiveness during audits.
What you should do now1 - Schedule a Demo to learn more about OvalEdge2 - Increase your knowledge on everything related to Data Governance with our free Whitepapers, Webinars and Academy 3 - If you know anyone who'd enjoy this content, share it with them via email, LinkedIn, Twitter or Facebook. |
Deep-dive whitepapers on modern data governance and agentic analytics

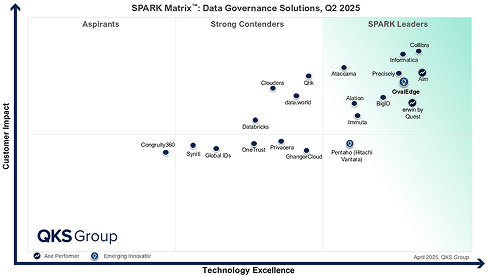
OvalEdge Recognized as a Leader in Data Governance Solutions
3ff1.png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
aef2.png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
Gartner, Magic Quadrant for Data and Analytics Governance Platforms, January 2025
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER and MAGIC QUADRANT are registered trademarks of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.