Table of Contents

Data Security in Snowflake: How OvalEdge Enables Secure Data Sharing & Governance
Data security in Snowflake protects cloud data through encryption, access control, governance, monitoring, and policy automation. Combining Snowflake security features with governance platforms helps organizations manage risk, enable secure sharing, and maintain compliance at scale
Introduction
Modern organizations depend on cloud analytics and shared data platforms. As companies move workloads into cloud warehouses, data security in Snowflake has become a top business priority.
Enterprises are no longer storing data in isolated systems. Instead, they operate collaborative ecosystems where analysts, data scientists, partners, and applications access the same datasets.
This rapid growth creates new risks. Companies must manage snowflake data security, maintain snowflake data privacy, and ensure proper snowflake data protection across thousands of users and datasets.
While Snowflake offers strong platform capabilities, managing security in Snowflake across business teams requires governance, ownership clarity, and automated policies.
A modern snowflake security data lake enables fast innovation, but without structured governance, organizations may face uncontrolled access, compliance risks, and data exposure.
Today, successful companies combine native platform controls with governance solutions that support snowflake data security and governance across the entire data lifecycle.
How Snowflake Data Security Works?
Snowflake provides a powerful foundation for data security in Snowflake environments. Its architecture protects data across storage, processing, and sharing layers.
1. Authentication and Identity Control
Snowflake supports secure authentication methods such as single sign-on, multi-factor authentication, OAuth, and key-based authentication. These controls ensure that only verified users enter the system.
2. Role-Based Access Control
Access permissions in Snowflake rely on role-based access control. Administrators assign roles that determine which users can view, edit, or share datasets. RBAC forms a critical component of Snowflake data security because it restricts unnecessary exposure.
3. Encryption and Data Protection
Snowflake automatically encrypts data both at rest and in transit. This built-in encryption strengthens Snowflake data protection and ensures sensitive information remains secure even during transfers.
4. Network Policies
Organizations can restrict connections based on IP ranges or private network rules. This reduces external risks and improves security in Snowflake environments.
5. Data Tagging and Classification
Snowflake allows tagging and classification of data objects. Tags help identify sensitive fields such as PII or financial data and enable policy enforcement aligned with Snowflake data privacy standards.
6. Monitoring and Auditing
Continuous logging and monitoring track user activity. Security teams can audit access patterns and identify unusual behavior, improving overall Snowflake data security and governance.
Snowflake delivers strong technical security controls. However, technology alone does not solve organizational governance challenges.
The Hidden Challenge: Why Snowflake Security Alone Is Not Enough?
Even with advanced controls, many enterprises struggle with data security in Snowflake after migration to the cloud.
The core issue is simple.
Platform security protects infrastructure. Governance defines business responsibility.
1. Platform Security Versus Governance
Snowflake secures the environment, but it does not always define who should access which data from a business perspective. Departments often maintain different definitions of sensitivity and ownership.
2. Missing Business Context
Data warehouses contain millions of attributes. Without classification policies, teams cannot consistently enforce snowflake data privacy requirements.
3. Access Chaos
As organizations grow, access requests increase rapidly. Manual approvals lead to delays or over-permissioning, weakening Snowflake data security.
Human error and excessive access permissions contribute to over 95% of data breaches
Also Read: Master Snowflake Access Management for Secure Data Sharing
4. Data Ownership Confusion
Many enterprises cannot clearly identify data owners or stewards. Without ownership, enforcing snowflake data protection becomes difficult.
These challenges explain why companies seek governance platforms that extend security in Snowflake beyond technical controls.
The Governance Layer: Role of Metadata and Data Governance
To achieve enterprise-grade data security in Snowflake, organizations must introduce a governance layer powered by metadata.
1. Metadata Control Layer
Metadata describes data structure, lineage, ownership, and sensitivity. When centralized, metadata becomes the control system for Snowflake data security and governance.
2. Policy Orchestration
Governance platforms automate classification, access approvals, and monitoring using metadata intelligence. Policies become consistent across the entire Snowflake security data lake.
3. Enterprise Governance Model
A mature governance model includes administrators, stewards, custodians, and business users working together under defined responsibilities.
This model transforms snowflake data security from reactive protection into proactive risk management.
This is where governance solutions like OvalEdge play a strategic role.
How OvalEdge Enables Secure Data Sharing in Snowflake?
OvalEdge strengthens data security in Snowflake through four core pillars that combine governance with automation.
1. Classification
Classification is the foundation of Snowflake data security. OvalEdge automatically scans data environments and categorizes datasets horizontally by department and vertically by sensitivity level.
Horizontal classification aligns data with business functions such as Finance, HR, or Sales.
Vertical classification identifies sensitive categories, including confidential, regulated, or personal information.
AI-driven classification ensures policies scale across growing data environments while supporting Snowflake data privacy standards.
2. Roles and Responsibilities
OvalEdge connects governance roles with Snowflake permissions. Administrators define approval workflows, while stewards oversee compliance and usage.
Two-way synchronization maintains alignment between governance policies and Snowflake access roles, strengthening Snowflake data security and governance.
3. Protection Through Masking and Restrictions
OvalEdge enables dynamic masking and policy-based restrictions. Sensitive information can be protected before it reaches the warehouse, improving snowflake data protection across internal analytics and external sharing scenarios.
4. Continuous Monitoring
Security must evolve with data growth. OvalEdge continuously monitors new datasets, triggers approval workflows, and logs access activity. This ensures ongoing security in Snowflake environments.
Architecture: How OvalEdge Integrates with Snowflake
OvalEdge integrates directly into the Snowflake ecosystem to operationalize data security in Snowflake.
|
Integration Capability |
Description |
Security Benefit |
|
Metadata Sync |
Syncs metadata between systems |
Central governance visibility |
|
Tag Synchronization |
Transfers classifications and tags |
Automated policy enforcement |
|
Policy Enforcement |
Applies masking and access rules |
Consistent protection |
|
Access Lifecycle |
Manages approvals and auditing |
Reduced operational risk |
Through this architecture, organizations create a governed snowflake security data lake that balances accessibility with control.
Benefits of Using OvalEdge with Snowflake
Combining governance automation with Snowflake capabilities delivers measurable outcomes that improve both security and business agility.
1. Faster access approvals improve analyst productivity
OvalEdge automates data access workflows based on classification and predefined policies. Analysts no longer wait for manual approvals, allowing teams to access trusted datasets quickly while maintaining strong data security in Snowflake without slowing innovation.
2. Automated policies strengthen security in Snowflake
Policy automation ensures consistent enforcement of masking, access controls, and governance rules. Instead of relying on manual administration, organizations maintain continuous security in Snowflake as new datasets, users, and workflows are introduced.
3. Reduced compliance risks across enterprise datasets
OvalEdge continuously monitors sensitive data and enforces governance standards aligned with regulatory requirements. Automated classification and auditing reduce human error and help organizations demonstrate compliance while improving overall Snowflake data protection.
4. Improved trust in analytics outputs
When users understand data ownership, lineage, and sensitivity levels, they gain confidence in analytics results. Governance visibility provided by OvalEdge enhances trust, ensuring business decisions rely on accurate and properly governed Snowflake data.
5. Consistent snowflake data security and governance across tools
OvalEdge extends governance beyond a single platform. Policies, roles, and classifications remain consistent across data tools and environments, creating unified snowflake data security and governance across the entire modern data ecosystem.
Organizations move from manual control to scalable, intelligent governance that supports secure collaboration and long-term data growth.
OvalEdge vs Native Snowflake Security
|
Capability |
Native Snowflake |
With OvalEdge |
|
Infrastructure Security |
Yes |
Yes |
|
Encryption |
Yes |
Yes |
|
Role Management |
Technical roles |
Business-aligned governance |
|
Data Classification |
Limited automation |
AI-driven classification |
|
Access Approval Workflow |
Manual |
Automated |
|
Continuous Governance |
Partial |
End-to-end |
|
Enterprise Visibility |
Limited |
Unified governance layer |
Native controls secure the platform. OvalEdge operationalizes data security in Snowflake across people, processes, and policies.
Best Practices for Data Security in Snowflake
- Classify all data assets before granting access.
- Align access policies with business ownership.
- Automate masking for sensitive fields.
- Monitor data usage continuously.
- Maintain centralized governance metadata.
- Audit permissions regularly to prevent privilege creep.
- Combine Snowflake security features with governance automation.
Following these practices strengthens long-term snowflake data protection and improves organizational trust in shared data environments.
Related:How End-to-End Data Governance in Snowflake Supports Business Agility
How OvalEdge tackles security challenges in Snowflake?
Four pillars of secure data access
The four areas of data security that the OvalEdge platform addresses in Snowflake are classification, roles and responsibilities, data protection, and monitoring. Together, they create a complete strategy for Data Security in Snowflake and govern secure data sharing in Snowflake.
Classify → Define Roles and Responsibilities → Protect → Monitor
1. Classification
Data classification is the critical first step for enforcing role-based access and is the cornerstone of Data Security in Snowflake. First, you will divide your data horizontally.
This is relatively easy as horizontal classifications are based on various business functions, such as Sales, HR, Marketing, and Finance.
With this methodology, the implementation is relatively more straightforward. You must be able to find some common thread to classify your data based on applications, databases, etc.
With horizontal classification, assigning access owners for various categories becomes easy.
The second task is to classify the data vertically. Vertical classification divides the data into categories like PII-Generic, PII-Complaint, Confidential, Top Secret, Standard, and Unidentified.
All data that is not yet classified will come under Unidentified Data. Vertical classification is an intricate process involving these steps:
- The first step is for the data/access owners of the horizontally classified data to make policies determining what data will fall under which category within their department.
- For example, deal size and total revenue within the Sales department could fall under ‘confidential.’ The commission earned by a sales rep on a deal could fall under ‘top secret.’
- Some categories will follow the same conventions across various departments.
PII-Generic: First name, last name, email
PII-Compliant: SSN, driver's license number
- The next step is to define role-based access policies for all the categories of fully classified data.
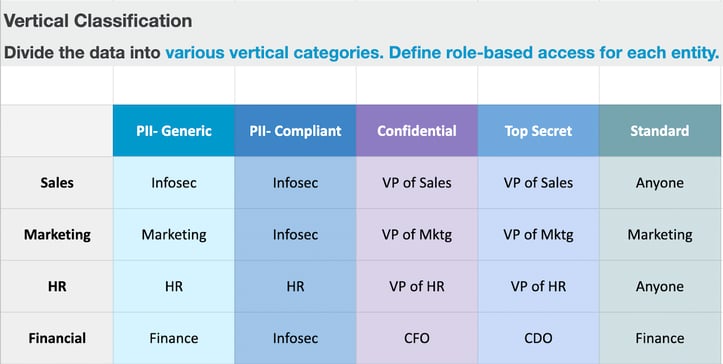
Example Matrix
OvalEdge enables customers to write policies for each classification, use AI to classify the data, and automatically enforce policies as data is classified. OvalEdge syncs these classifications directly with Snowflake to enforce tag-based security automatically, a prerequisite for any secure data sharing in Snowflake.
2. Roles and Responsibilities
Once organizations have classified their data in OvalEdge, they must design an approval process based on these classifications. The various data governance roles and responsibilities in an organization support access policies.
Data governance roles usually include admin, steward, custodian, and user. These roles carry various responsibilities, and while a user may only have access to limited data sets, an admin will have the power to designate access to others.
Our platform Ovaledge supports two-way syncing of these user roles and permissions with Snowflake, which is essential for managing permissions across the data landscape and for governing secure data sharing in Snowflake.
3. Protect: Masking and Restricting Sensitive Data
To prevent unauthorized access, a core goal of Data Security in Snowflake sensitive information must be protected. OvalEdge allows you to define policies that automatically mask or restrict data based on a user's role.
This data protection can be applied at the source, before the data even reaches your Snowflake data warehouse, ensuring raw sensitive data is never exposed, whether in internal use cases or in secure data sharing in Snowflake with external parties.
4. Monitor: Continuous Security Assurance
Data Security in Snowflake is not a one-time event. OvalEdge provides continuous data monitoring. Whenever new data is detected, our AI automatically triggers an approval request to the relevant data owner or steward.
This ensures your data access security measures are consistently maintained, even as your data ecosystem evolves, safeguarding all operations, including dynamic secure data sharing in Snowflake.
Conclusion
Modern cloud analytics requires more than technical safeguards. True data security in Snowflake combines platform security with governance, ownership, and continuous monitoring.
Snowflake delivers powerful infrastructure protection, encryption, and access control capabilities.
However, organizations achieve scalable snowflake data security and governance only when policies align with business context and data lifecycle management.
Ovaledge helps enterprises bridge this gap. By automating classification, synchronizing roles, enforcing protection policies, and enabling continuous monitoring,
Ovaledge transforms Snowflake into a secure, governed, and collaborative data ecosystem.
If your organization wants to enable trusted analytics, safe data sharing, and enterprise-grade governance, Ovaledge provides the framework to operationalize secure data management across your Snowflake environment.
FAQs
1. What is Data Security in Snowflake?
Data Security in Snowflake refers to the processes, controls, and governance practices that protect sensitive data stored or shared within Snowflake. This includes access policies, masking, classification, encryption, and monitoring.
2. How does OvalEdge improve secure data sharing in Snowflake?
OvalEdge automates data classification, role-based access, masking, and approval workflows. This ensures only authorized users can view or share sensitive Snowflake data.
3. Why is data classification important in Snowflake?
Without classification, organizations cannot enforce consistent access rules. Classification enables tag-based policies, masking, and compliant data sharing.
4. Can Snowflake handle enterprise-level security on its own?
Snowflake provides strong platform-level controls, but enterprise teams still need external governance tools (like OvalEdge) to define business-aligned policies and determine who should access what.
5. How does OvalEdge sync with Snowflake?
OvalEdge performs two-way syncing of metadata, roles, permissions, classifications, and tags to maintain consistent governance across both platforms.
6. What kind of data can be masked using OvalEdge?
OvalEdge can mask PII, financial data, healthcare data, employee-level data, and any custom classified field.
7. Does OvalEdge support auditing and monitoring?
Yes. OvalEdge automatically sends approval requests and logs all access events, ensuring continuous oversight.
8. Is secure data sharing in Snowflake suitable for large enterprises?
Yes. With proper governance tools like OvalEdge, enterprises can safely scale secure data sharing while maintaining compliance and reducing operational risk.
What you should do now
|
Deep-dive whitepapers on modern data governance and agentic analytics

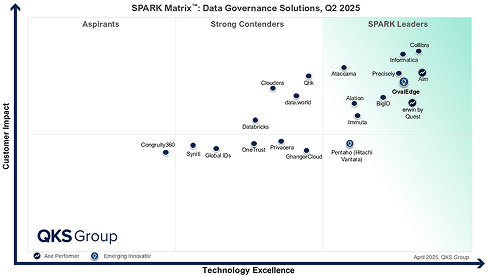
OvalEdge Recognized as a Leader in Data Governance Solutions
3ff1.png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
aef2.png)
“Reference customers have repeatedly mentioned the great customer service they receive along with the support for their custom requirements, facilitating time to value. OvalEdge fits well with organizations prioritizing business user empowerment within their data governance strategy.”
Gartner, Magic Quadrant for Data and Analytics Governance Platforms, January 2025
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
GARTNER and MAGIC QUADRANT are registered trademarks of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.